Boost Security, Simplify Connectivity: All with SASE
Table of Contents:
- Understanding SASE and Its Significance in Modern Security Architecture
- The Evolution of Network Security: From Perimeter-Based Defenses to SASE
- Critical Components of SASE Architecture
- The Benefits and Challenges of Implementing SASE
- Real-Life Case Studies: SASE in Action
- Future-Proofing Your Organization with SASE
- Comparing SASE Providers: What to Look For
- Integrating SASE with Existing Security Measures
- SASE and Compliance: Navigating Regulatory Challenges
- Best Practices for SASE Implementation and Optimization
Key Takeaways:
- SASE is a cloud-based security and network service which delivers the convergence to the center.
- SASE implementation covers many use cases like better security, better internet connection, and making compliance a lot easier.
- Developing strategy and choosing the best available tools are two key elements of comprehensive cause adoption.
Understanding SASE and Its Significance in Modern Security Architecture
Digital environment covers the ever-growing cloud services and mobile devices; because of that, old protection techniques can not secure such a multi-faced virtuality. The SASE (Secure Access Service Edge) solution brings to the game the flair of the cloud architecture and resourcefulness of cloud-native technology with an insistence on impeccable security. This holistic cybersecurity approach answers to the absence of enterprise perimeter limits that makes the solution layer that forms a unified-coverage and precise-control-mechanisms fabric.
Integrating SASE technologies is an architectural revolution in which the cloud-based network services are combined with the security-of-services principles. SASE achieves intertwined security for access that is not crucial to be separated to the network location but can be rather distributed throughout the platform on a user-granted basis. This shift of paradigm is most vital for organizations implementing a work-from-anywhere philosophy, as well as those making use of a complex constellation of on-premises and cloud-based assets.
The Evolution of Network Security: From Perimeter-Based Defenses to SASE
In the past, network security was a stronghold and the guards had to forbid any intruders to get to its property. The boundary-based defense nevertheless may seem to be less crucial when the user along with their systems moved towards outside such limits. SASE stands for Secure Access Service Edge and represents a gradual shift towards a collaborative security model that validates users and persistent devices wherever they are at a certain moment. This acceptance that work is not a location to be gone too but a thing to be done at anytime, anywhere, with immediateness and pervasiveness, has become a basis for a new security aspect.
SASE doesn’t only mend up the traditional perimeter security anymore. By no means it implements a new model. Putting together the advanced security measures on the top of the software-defined network and presenting it with global unification to various scenarios, we offer the access control device which is as granular and precise as possible. The morphing of this security landscape is not only a rejuvenation, but is a reinvention in which it will keep up with the fast pace of digital transformation together with the growing diversity of edge computing.
Critical Components of SASE Architecture
SASE brings together a number of technologies that were originally independently developed but are now linked to create a single SASE framework with specialized goals. CASB (Cloud Access Security Broker) is an example of a core component that allows visibility and control over cloud-based applications, and SD-WAN (Software-Defined Wide Area Network) which is used to facilitate the routing of the network traffic is another side of the connection. The essence of the Zero Trust Architecture (ZTA) should never be to assume trust while it is also to validate everything unforgivingly. On the other hand, the FWaaS offerings defend against the network internal and external threats within the real time. Eventually, Secure Web Gateway (SWG) denies users from malware & virus as well as enforces institutional and acquired regulations, rounding off the entire SASE nature.
The essential feature of SASE involves an approach that is multifaceted in being able to accommodate different and complex security needs in a service that is created as a unified and streamlined product, as a reason for such.
The Benefits and Challenges of Implementing SASE
Organizations sponsoring SASE will have a series of expected advantages across the board. They include the standard security machinery, better network operation and improvement of performance due to cloud access clients and a cost-cutting process that is brought about by minimization of the dependency on the legacy hardware. Despite the fact that there are numerous perks, businesses need to acquire some assistance to adopt the SASE approach. It can also be tough to accommodate new members to replace ones you know. When it comes to implementing a coherent SASE strategy, it’s one thing to integrate new components, but quite another thing to involve legacy systems.
Firstly, championing the cause and acquiring management commitment is essential. Secondly, this has to be followed by leadership and the adoption of the culture shift within IT sections. An organization should not look at introducing SASE tantamount of change in security technology but as part of a transformed system where security is integrated in operational procedures of the organization.
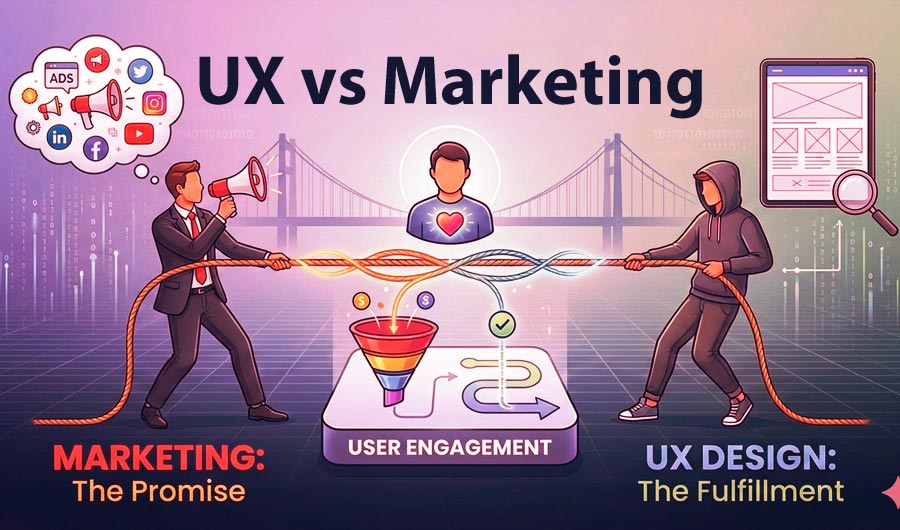
Real-Life Case Studies: SASE in Action
Case studies from industries where SASE has been implemented are a great method to highlight its real-world usefulness. Thus, enterprises have reported a drop in security breaches after being SASE compliant. Reason being the easier to detect and respond to the threats. SASEs being able to give access control without reference to users location is a capability that is a must have for companies with staff with transnational repost media. Additionally, their organizations report that SASE enables scaling of security functions with organization growth easier. SASE works perfectly with development teams practicing agile. That way the security part of applications has no barriers to support continuous update models.
Future-Proofing Your Organization with SASE
When it comes to fighting future cyber threats, the best attitude to embrace is one that always expects the unexpected and is ready to meet any new and emerging challenges within seconds. The SASE is an education method which deals with the present demands while innovating and building an infrastructure committed to meeting future requirements. By the dint and power of SASE’s scalability and adaptability, organizations can make sure that their security architecture is constantly growing and phasing along with time in order to be one step ahead of potential risks.
Comparing SASE Providers: What to Look For
When inspection of possible SASE providers is the motive, fixating on those ones who provide a broad base of services and can be customized to match organization’s specific necessities is a significant consideration. This is where we have to assess the provider’s history of innovation, answer to customer care and the capabilities that make it viable and possibly join with what you have. Figuring out which vendor offering the best ZTNA or SD-WAN service will have implications as to how these services can be used and carried out to improve the implementation of the SASE.
Integrating SASE with Existing Security Measures
Identifying the challenges and considering the multi-faceted impact is the critical task for the organization when making the switch to a SASE model and ensuring the efforts do not disrupt operations. Ensuring that this transition remains orderly and integrated needs a paramount concern where our systems currently run would be adjusted to effectively collaborate with SASE solutions. Certainly keeping that in mind, it is the question of thorough employee training on newly adopted security and productivity protocols which will provide for the transition.
SASE and Compliance: Navigating Regulatory Challenges
SASE exemplifies in its simple control mechanism one of the most important benefits within the sphere of an emptying compliance environment: easy-to-understand agreements and less paperwork. Distracted network activities such as monitoring of traffic, application of security policies, and recording activities will have a sensational effect on organizational adherence to standards and regulations; thus SASE can reduce compliance burden this way.
Best Practices for SASE Implementation and Optimization
Proper implementation of ABM depends on the adoption of the aforementioned best of the breed practices. This further refines the process. It is important to note specifically that a good knowledge of the telecommunication network architecture together with proper understanding of the scope of requirements is very key. The organization’s proactivity regarding performance monitoring and a vision to calibrate back approaches about the SASE utilization, establish the organization’s desire to achieve the highest SASE potential.